Energy token operators
These are the natural first users of Energy-token workflows on Kaspa.
- Solar Installers
- Energy Monitoring Providers
- Inverter Manufacturers
- Solar Farms
- Crypto Mining Farms
Launch energy tokens and custom measured-workflow apps with Compliance Wallet. Add Compliance Node when you need broker, market-maker, and regulated-asset controls.

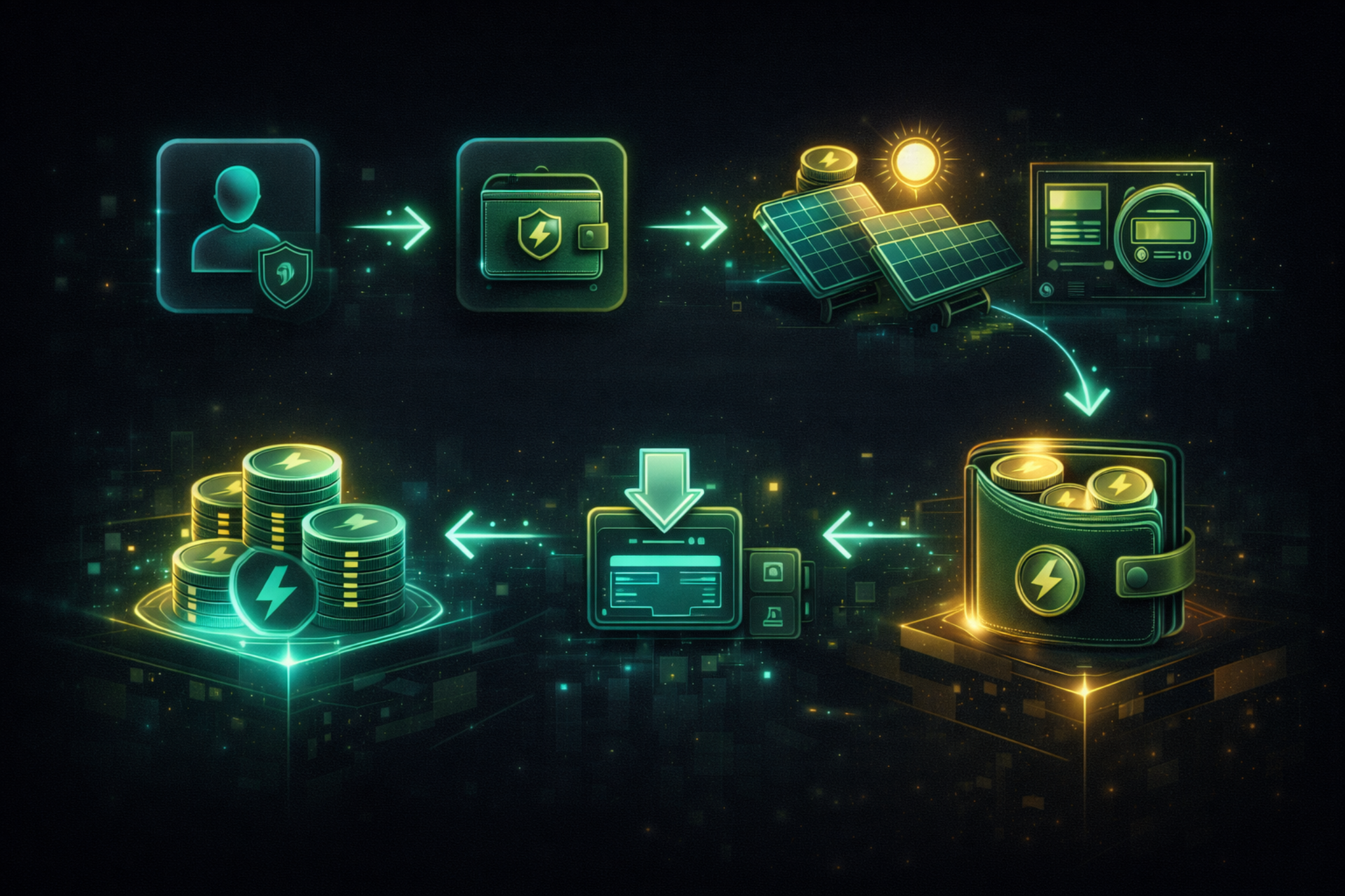
The strongest first workflow in CW/CN v1 starts with Energy. A new operator can sign up, deploy an Energy token, add a measured site, download production, and begin issuing KWH-backed balances through a guided flow that uses the full platform.
Enter the product, create the right wallet set, and establish the user-side operating identity.
Launch a token for measured production and lock it into the Energy workflow where it belongs.
Connect a measured site, download production, and issue Energy-backed balances into the wallet.
CW/CN v1 is designed for operators who need real tokenized workflows, not just wallet screenshots. The first public example is Energy, but the platform is broader than one vertical.
These are the natural first users of Energy-token workflows on Kaspa.
These are the organizations that benefit from policy, distribution, and controlled market access.
CW/CN v1 is the working baseline today: wallets, token operations, swaps, compliance-aware participation, notifications, and Energy issuance. From here, the roadmap expands into operator intelligence, programmable policy, and stronger market infrastructure around the same core platform.
Working user wallets, token issuance and burn, direct and open swaps, Compliance Only flows, notifications, and Energy issuance.
Discovery, alerts, operator intelligence, and revenue-driving services built on top of the live CW/CN product.
Deeper policy automation, broader market structure, stronger custody options, and more custom tokenization workflows.


Energy is the first public story because it is the strongest hook and the most complete user workflow. But the platform is broader. If your business has measurable production, inventory, usage, throughput, or policy-gated rights, CW/CN can be shaped into custom tokenization flows that fit how your operation actually works.
CW/CN v1 is already a usable product baseline for demos, pilots, recorded flows, and early operator conversations.
Standard Wallets, Compliance Wallets, whitelist controls, send/receive, and lifecycle actions.
Deploy, import, issue, burn, and Energy-token workflows already operate in the product.
Direct swaps, open swaps, Analyzer views, and Compliance Only offer logic are already working.
CN policy effect, notifications, and regulated-path differentiation are visible in the live system.
Request access, schedule a guided demo, or talk with us about an Energy-token pilot, broker-assisted regulated distribution, or a custom tokenization app built around measurable real-world output.